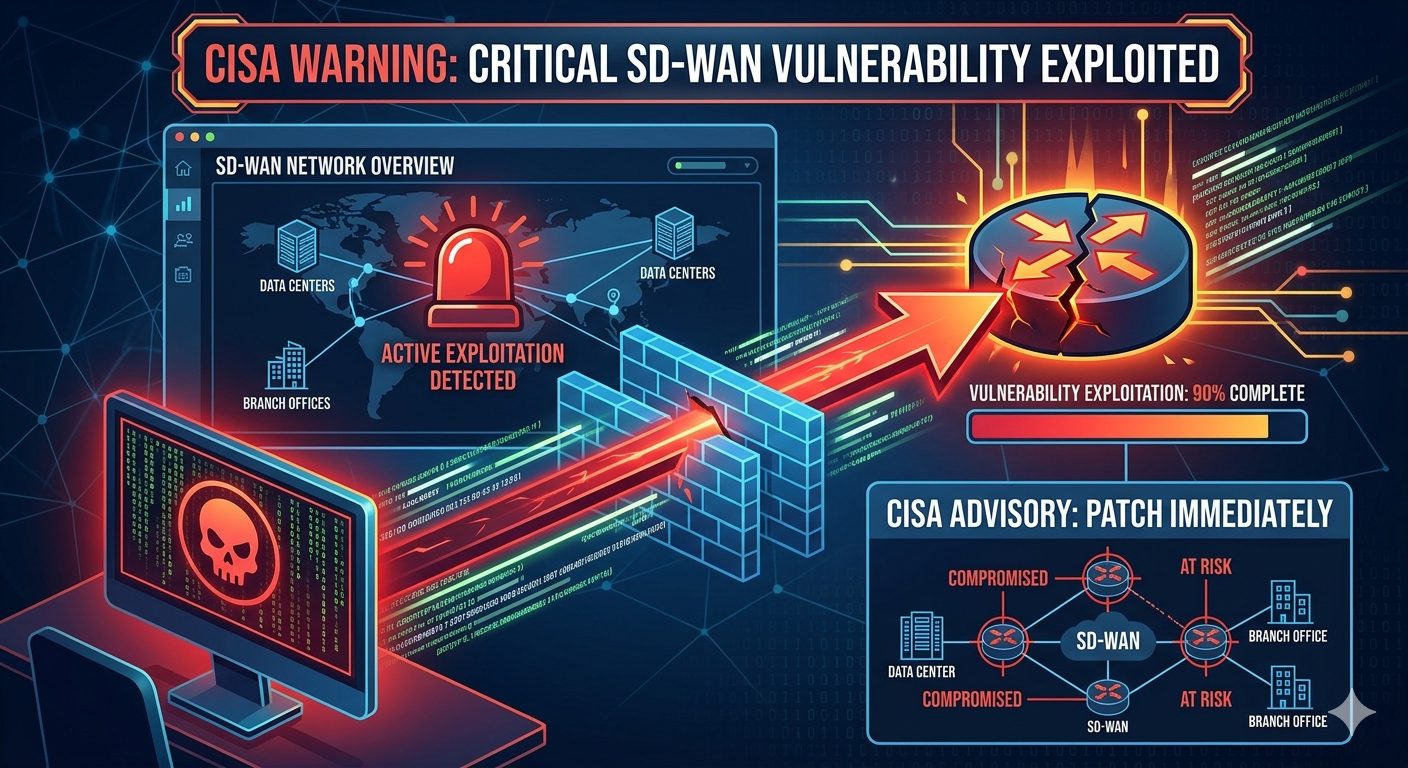
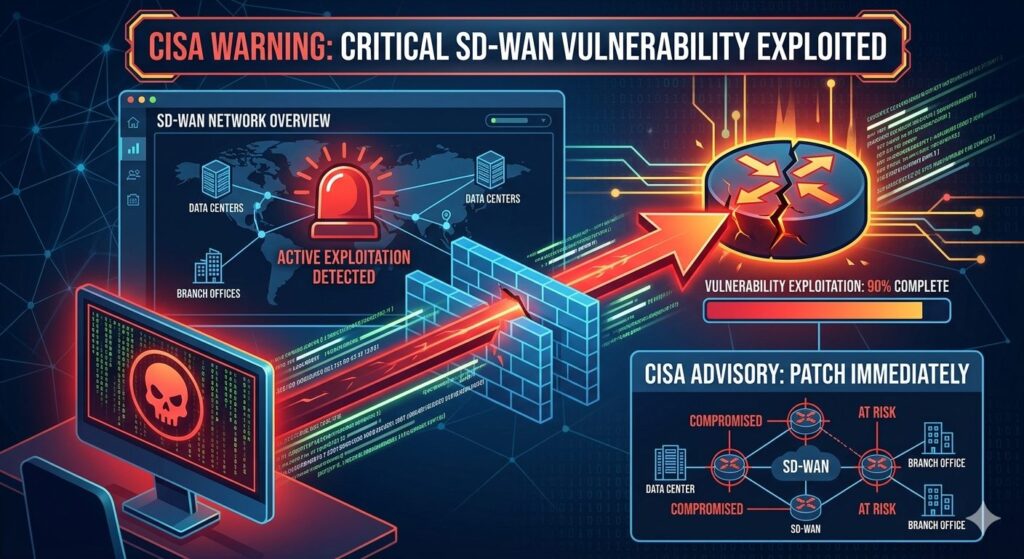
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned that a newly discovered Cisco Catalyst SD-WAN Manager vulnerability (CVE-2026-20133) is being actively exploited, urging federal agencies to patch systems by April 24, 2026. The flaw allows unauthenticated attackers to access sensitive information, posing serious risks to organizations using unpatched devices.
Key Highlights
- Vulnerability: CVE-2026-20133 in Cisco Catalyst SD-WAN Manager (formerly vManage).
- Impact: Enables unauthenticated remote attackers to read sensitive information from the underlying operating system.
- Cause: Insufficient file system access restrictions.
- Deadline: U.S. federal agencies must patch by Friday, April 24, 2026.
- Status: Cisco released a patch in February 2026, but exploitation in the wild has now been confirmed by CISA.
Background
- Catalyst SD-WAN Manager is a centralized tool used to monitor and manage up to 6,000 Cisco SD-WAN devices.
- In February 2026, Cisco patched multiple vulnerabilities, including CVE-2026-20133, CVE-2026-20128, and CVE-2026-20122.
- Shortly after, Cisco acknowledged that two of these flaws were already being exploited.
- CISA has now added CVE-2026-20133 to its Known Exploited Vulnerabilities (KEV) Catalog, confirming active attacks.
CISA’s Directive
- Agencies must follow Emergency Directive 26-03 and Hunt & Hardening Guidance for Cisco SD-WAN Devices.
- If mitigations are not possible, discontinue use of the product.
- This directive is part of CISA’s broader effort to reduce exposure to exploited Cisco vulnerabilities—91 Cisco flaws have been flagged in recent years, with several linked to ransomware campaigns.
Cisco’s Position
- Cisco’s Product Security Incident Response Team (PSIRT) has not yet confirmed public exploitation of CVE-2026-20133.
- However, CISA’s evidence of active exploitation has prompted urgent action.
- Cisco continues to release updates for other critical flaws, including authentication bypass and Secure Firewall Management Center vulnerabilities.
Risks for Organizations
- Data Exposure: Attackers can access sensitive system information.
- Network Compromise: Exploitation could lead to deeper infiltration of enterprise networks.
- Ransomware Threats: Past Cisco vulnerabilities have been leveraged by ransomware groups.
Recommended Actions
Monitor for suspicious activitypikes.
✔ Avoid unofficial app sources and suspicious modified apps to reduce risk.
Patch immediately using Cisco’s February 2026 update.
Audit SD-WAN deployments for exposure.
Follow CISA’s hardening guidance to reduce attack surface.