Microsoft April 2026 Patch Tuesday: 167 Vulnerabilities Fixed, Including 2 Zero-Days
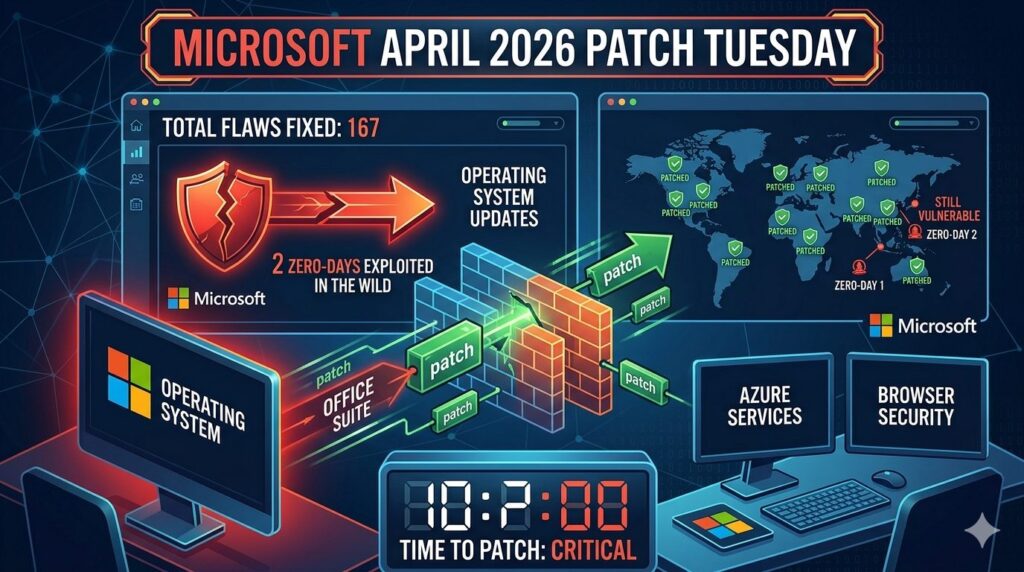
🚨 Microsoft April 2026 Patch Tuesday Fixes 167 Vulnerabilities The Microsoft April 2026 Patch Tuesday update fixes 167 security vulnerabilities across Windows, Office, and SharePoint systems. This update also includes 2 zero-day vulnerabilities, which makes it critical for organizations to apply patches immediately. 🔍 Key Highlights of Microsoft April 2026 Patch Tuesday The Microsoft April […]
OpenAI Launches GPT-5.4-Cyber for Advanced Cybersecurity Defense
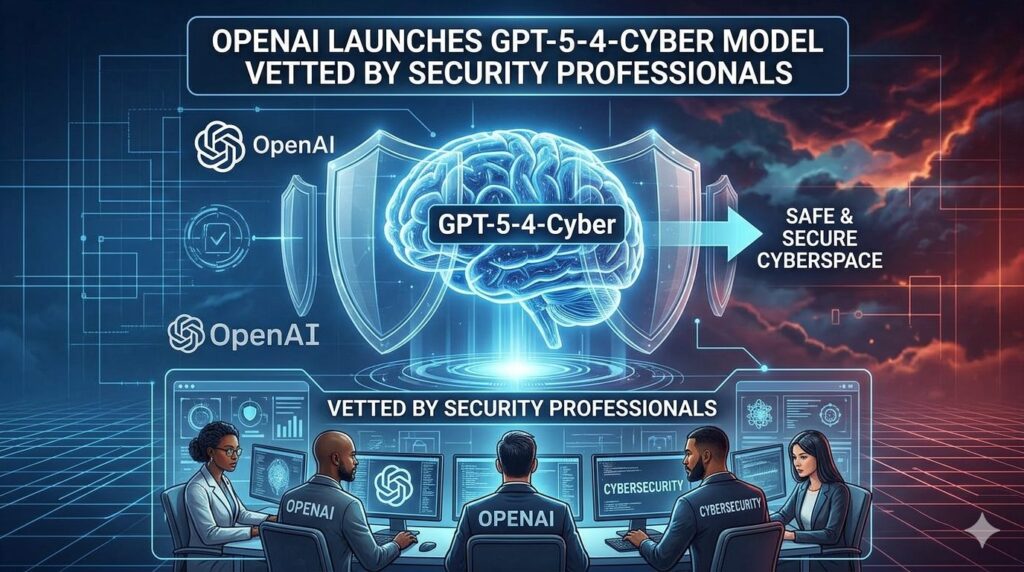
🚨 AI Meets Cybersecurity: OpenAI Introduces GPT-5.4-Cyber OpenAI has unveiled GPT-5.4-Cyber, a specialized AI model built specifically for cybersecurity professionals—marking a significant step forward in how organizations defend against increasingly complex digital threats. 🔍 What makes GPT-5.4-Cyber different?Unlike general-purpose AI models, GPT-5.4-Cyber is fine-tuned for defensive security operations. It is designed to assist experts in […]
CISA Warns of Actively Exploited Cisco SD-WAN Vulnerability
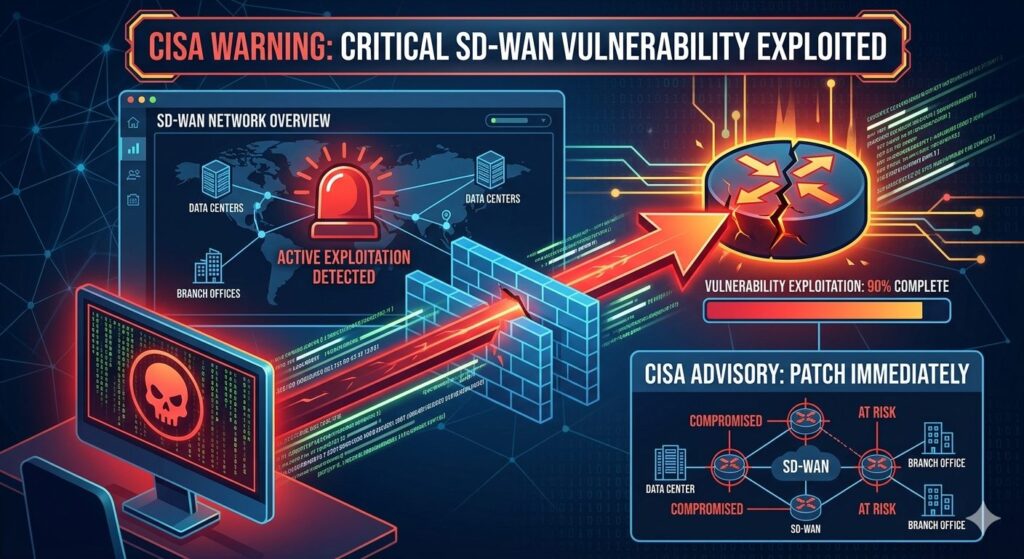
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned that a newly discovered Cisco Catalyst SD-WAN Manager vulnerability (CVE-2026-20133) is being actively exploited, urging federal agencies to patch systems by April 24, 2026. The flaw allows unauthenticated attackers to access sensitive information, posing serious risks to organizations using unpatched devices. Key Highlights Background CISA’s […]
New Android Malware Uses AI to Click Hidden Browser Ads

📌 What Is It? A newly spotted family of Android malware is using artificial intelligence (AI) to perform click-fraud — i.e., automatically generating fake ad clicks to make money for attackers. Unlike older malware that used scripted rules, this one leverages machine learning to visually identify ads and interact with them, mimicking real user behavior. […]
Microsoft Confirms Windows 11 Lock Screen Password Option Bug in Recent Updates

Microsoft has issued a warning to Windows 11 users regarding a user interface bug introduced by updates released since August 2025, which may cause the password sign-in option to disappear from the lock screen. Although the option is not visibly displayed, Microsoft confirmed that the password sign-in feature remains functional. How Sign-In Options Normally Work […]
New Android Malware ‘DroidLock’ Can Hijack Phones in Real TimeHackers exploit newly patched Fortinet auth bypass flaws

📌 What DroidLock Is DroidLock is a newly identified type of Android malware that behaves like ransomware but is even more dangerous because it gives attackers near-total control over infected phones. Rather than encrypting files like traditional ransomware, DroidLock aggressively abuses Android system permissions and overlays to lock the device and extort victims. 🛠️ How […]
Hackers exploit newly patched Fortinet auth bypass flaws

Critical Fortinet Vulnerabilities Actively Exploited CVE-2025-59718 & CVE-2025-59719 Executive Summary Threat actors are actively exploiting two critical-severity authentication bypass vulnerabilities affecting multiple Fortinet products. These flaws allow attackers to gain unauthenticated administrative access via FortiCloud Single Sign-On (SSO) and exfiltrate system configuration files, potentially enabling further compromise of enterprise networks. Fortinet disclosed these vulnerabilities on […]
Google Patches Sixth Chrome Zero-Day Exploited in 2025 Attacks

Google has released an emergency security update to fix a new zero-day vulnerability in its Chrome web browser, marking the sixth actively exploited flaw patched this year. The Vulnerability Security Update Zero-Days in 2025 This latest fix adds to a growing list of Chrome zero-days exploited this year: In 2024, Google patched 10 additional zero-day […]
How attackers are still phishing “phishing-resistant” authentication
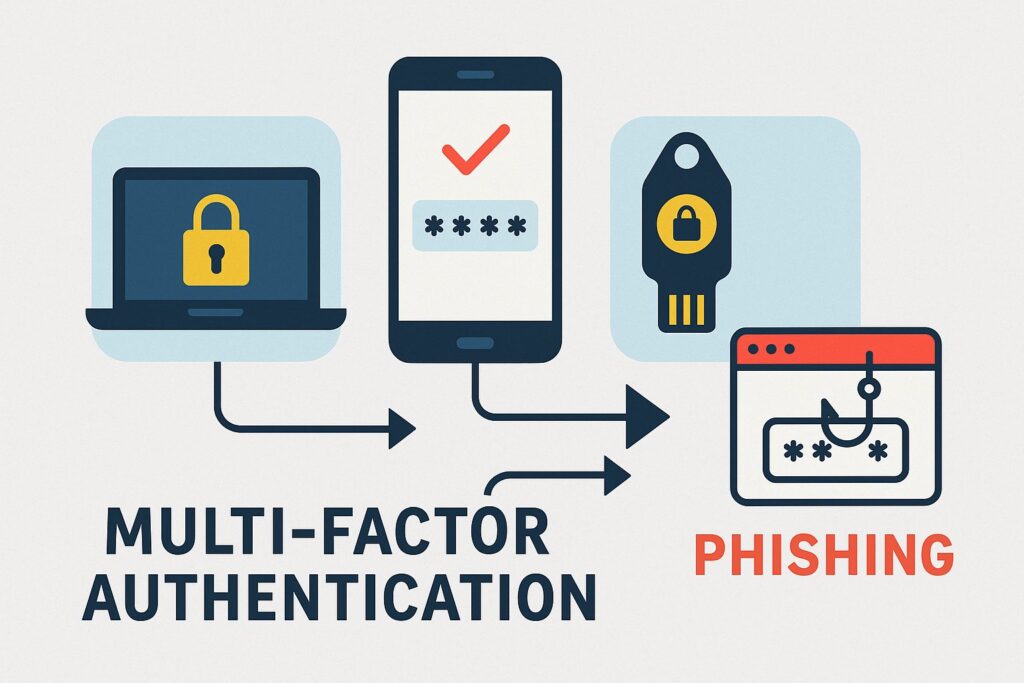
🔐 Overview Despite the rise in phishing‑resistant authentication methods such as FIDO2-based passkeys, WebAuthn, Windows Hello, and physical security keys attackers continue to successfully bypass them using more sophisticated phishing techniques. 🧪 Attack Techniques Used 1. Downgrade Attacks 2. Device‑Code Phishing 3. Consent Phishing (OAuth Abuse) ⚖️ Why These Methods Still Work ✅ Mitigation Strategies […]
16 billion passwords exposed in record-breaking data breach
The massive excitement around Artificial Intelligence (AI) tools has become a goldmine for cybercriminals. They’re heavily using this buzz to trick people into downloading dangerous ransomware and malware. This isn’t just a tactic for highly advanced hackers anymore; even smaller, lesser-known groups are now effectively using this strategy. These malicious actors, including ransomware gangs like […]
