Google Patches Sixth Chrome Zero-Day Exploited in 2025 Attacks

Google has released an emergency security update to fix a new zero-day vulnerability in its Chrome web browser, marking the sixth actively exploited flaw patched this year. The Vulnerability Security Update Zero-Days in 2025 This latest fix adds to a growing list of Chrome zero-days exploited this year: In 2024, Google patched 10 additional zero-day […]
The Great Firewall Data Leak: A Global Wake-Up Call for Cybersecurity Governance

In a striking development that underscores the fragility of digital sovereignty, over 500 gigabytes of internal data from Geedge Networks—a key contractor behind China’s Great Firewall (GFW)—was recently leaked online. This breach has revealed not only the technical architecture of one of the world’s most sophisticated internet censorship systems, but also the broader geopolitical implications […]
CVE-2025-43300 vulnerability :Understanding Apple’s ImageIO Framework

Introduction Apple’s ecosystem is well-known for its seamless user experience. One of the unsung heroes behind this smooth interaction with digital images is the ImageIO Framework. This framework provides developers with a standardized way to read, write, and process image files across iOS and macOS. While ImageIO makes handling images efficient and reliable, it is […]
NCSA Urges Immediate Update to iOS 18.6.2 and iPadOS 18.6.2 Following Discovery of Critical Vulnerability
The National Cyber Security Agency (NCSA) of Thailand has issued an urgent advisory for all users of iPhone and iPad devices to promptly update to iOS 18.6.2 and iPadOS 18.6.2, following the identification of a critical security vulnerability tracked as CVE-2025-43300 within Apple’s ImageIO Framework. This vulnerability, classified as a zero-day, has reportedly been exploited in targeted attacks. According to Apple’s official security […]
Outsourcing Without Oversight: PDPA Penalties Hit Healthcare Sector

On August 1, 2025, Thailand’s Personal Data Protection Committee (PDPC) issued a formal statement regarding a serious data breach involving a prominent private hospital. The incident has sparked widespread attention across social media and raised concerns about data governance in the healthcare sector. Incident Overview The hospital, acting as the Data Controller, had outsourced the […]
How attackers are still phishing “phishing-resistant” authentication
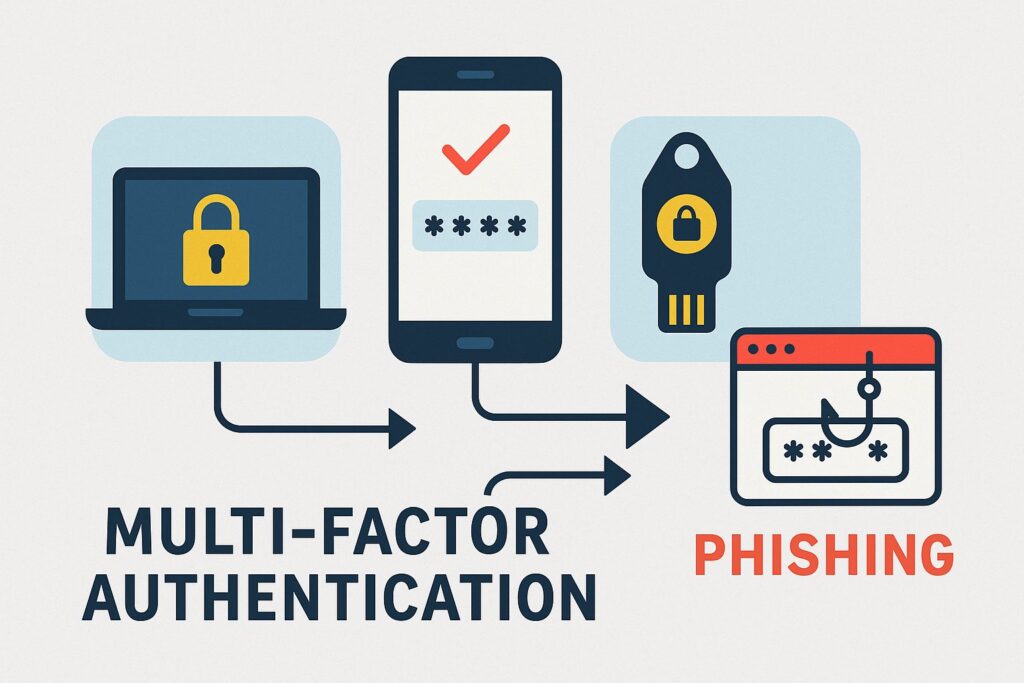
🔐 Overview Despite the rise in phishing‑resistant authentication methods such as FIDO2-based passkeys, WebAuthn, Windows Hello, and physical security keys attackers continue to successfully bypass them using more sophisticated phishing techniques. 🧪 Attack Techniques Used 1. Downgrade Attacks 2. Device‑Code Phishing 3. Consent Phishing (OAuth Abuse) ⚖️ Why These Methods Still Work ✅ Mitigation Strategies […]
Thailand Under Siege: What the Latest Cyber Attacks Mean for All of Us

I’ve been following cybersecurity news for years, but what’s happening in Thailand right now has me genuinely concerned. It’s not just another data breach or ransomware story – this feels different, more targeted, and frankly, more dangerous. What’s Really Going Down in Thailand Since March, Thai government systems have been getting absolutely pounded by hackers. […]
16 billion passwords exposed in record-breaking data breach
The massive excitement around Artificial Intelligence (AI) tools has become a goldmine for cybercriminals. They’re heavily using this buzz to trick people into downloading dangerous ransomware and malware. This isn’t just a tactic for highly advanced hackers anymore; even smaller, lesser-known groups are now effectively using this strategy. These malicious actors, including ransomware gangs like […]
How Hiring Managers Can Detect Resume Fraud: A Professional Guide

Resume fraud has become an increasingly pressing concern for HR professionals and hiring managers. Recent studies reveal that this issue is more pervasive than many organizations realize, with significant implications for hiring quality and workplace integrity. Understanding how to identify and prevent resume fraud is crucial for maintaining effective recruitment processes. The Growing Problem of […]
When AI Becomes a Double-Edged Sword: The EchoLeak Story

“Imagine a world where your personal and sensitive information could be leaked without you even lifting a finger. This is not a scene from a sci-fi movie, but a real threat discovered in Microsoft 365 Copilot. Welcome to the era of EchoLeak.” We live in a world where AI assistants have become our digital sidekicks, […]
